Perimeter Security Solutions for Correctional Institutions
Ensuring Safety and Preventing Escapes with Advanced Security Measures
Overview of Correctional Institutions with Security Needs and Effective Solutions
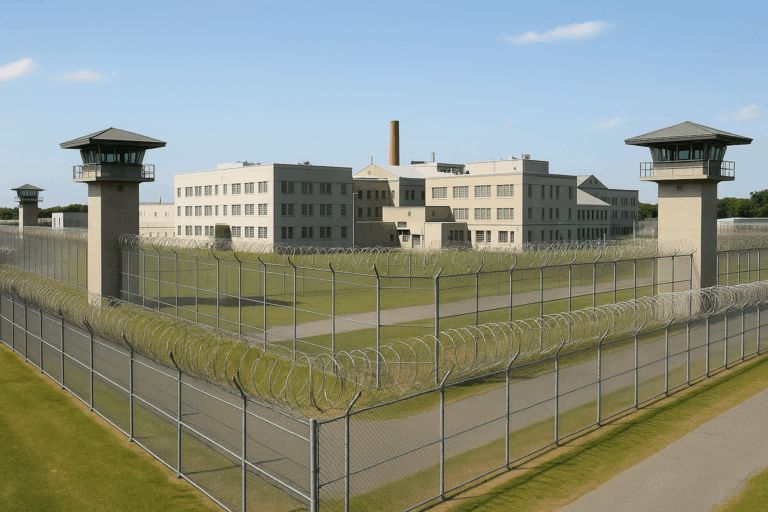
Correctional facilities are tasked with the critical responsibility of securely housing inmates while ensuring the safety of staff and the surrounding community. Implementing tough perimeter security measures is essential to prevent escapes, deter contraband smuggling, and maintain order within these institutions.
Page Content Navigation
Understanding Unique Challenges in Correctional Facilities
Customized Security Strategies for Correctional Facilities
Developing a Comprehensive Security Plan for Correctional Institutions

Understanding Unique Challenges in Correctional Facilities
Managing Large Perimeters
Correctional facilities often span expansive properties, requiring strategic planning to secure perimeter zones effectively. The size and layout of these perimeters can create vulnerabilities if not properly addressed with comprehensive coverage and reliable system performance.
Segmented Surveillance Zones
Dividing the perimeter into monitored sectors improves response times and helps teams quickly identify the location of potential threats or incidents.Power and Connectivity Infrastructure
Extending reliable power and network access to remote perimeter areas ensures continuous operation of cameras, sensors, and detection systems.Advanced Detection Technologies
Fiber optic sensors, buried cable systems, and fence-mounted detection help monitor long perimeters without requiring excessive manpower.Integrated Command Centers
Centralized monitoring platforms allow for unified control and situational awareness, linking surveillance feeds, alarm systems, and access controls.Routine Patrol Coordination
Augmenting technology with regular foot or vehicle patrols maintains a visible security presence and fills potential blind spots.
Effectively managing a large perimeter requires customized designs, integrated systems and smart resource allocation. By leveraging both technology and trained personnel, correctional facilities can maintain consistent security coverage across even the most complex environments.
Preventing Escapes and Unauthorized Access
Maintaining containment and controlling access are foundational to the security strategy of any correctional facility. Escape attempts and external breaches pose serious risks to public safety, facility operations, and staff well-being. A proactive perimeter security plan integrates physical infrastructure, technology, and training to detect, deter, and respond to threats before they escalate.
High-Security Fencing
Anti-climb, anti-cut perimeter fencing with integrated tamper detection serves as the facility’s first barrier to unauthorized movement. Many facilities reinforce these barriers with razor wire or concertina coils to maximize deterrence.Non-Lethal Electrified Fencing (Stun Fence)
Electrified fences deliver a pulsed high-voltage shock to deter climbing or tampering. These fences act as both a physical barrier and a real-time alert system when breached.Surveillance and Monitoring
Strategically placed cameras—enhanced with motion detection, night vision, and thermal imaging—provide around-the-clock visual coverage of all vulnerable perimeter zones.Controlled Access Points
Secure gates, sally ports, and turnstiles restrict movement into and out of the facility, especially during transitions such as staff changes and vehicle inspections.Intrusion Detection Systems
Ground sensors, vibration detectors, and fence-mounted alarms deliver real-time alerts when movement, cutting, or tampering is detected near the perimeter.Staff Readiness and Drills
Ongoing training and scenario-based drills prepare staff to respond quickly and decisively to any threat involving escape attempts or suspicious perimeter activity.
By combining advanced perimeter systems with disciplined procedures and vigilant personnel, correctional facilities can minimize escape risks and maintain strong operational security.
Contraband Control
Maintaining safety and order within correctional facilities depends heavily on controlling the flow of contraband. Unauthorized items—ranging from weapons and tools to drugs and communication devices—pose serious threats to staff, inmates, and overall facility stability. Effective contraband control requires layered protocols, advanced technology, and continuous vigilance.
Screening Procedures for Staff and Visitors
Comprehensive entry screenings using metal detectors, baggage scanners, and manual searches help intercept contraband before it enters the facility.Body Scanning Technology
Full-body scanners provide non-invasive imaging that detects concealed items on or within individuals, reducing reliance on manual pat-downs alone.Parcel and Mail Inspection
X-ray scanners and controlled mailroom protocols help prevent the smuggling of illicit materials through correspondence and package deliveries.Aerial Threat Detection
Drone surveillance and detection systems are essential to identify and intercept attempts to deliver contraband over fences via unmanned aerial vehicles.Inmate Housing Area Sweeps
Routine and unannounced searches of cells and common areas are critical to disrupting internal distribution and maintaining control.Visitor and Vendor Management Systems
Digital check-in and monitoring systems provide full visibility into who enters the facility and can flag suspicious behavior or repeat patterns.
By combining physical security, emerging technologies, and consistent enforcement protocols, correctional facilities can significantly reduce the risk of contraband-related incidents and reinforce the safety of both staff and inmates.
Internal and External Threat Assessments
Correctional facilities face a wide range of threats that originate both inside and outside their secure perimeters. Identifying and understanding these risks is essential for developing a proactive security strategy that addresses vulnerabilities before they become incidents. Threat assessments provide a structured framework for evaluating potential dangers and implementing appropriate countermeasures.
Inmate Behavior Monitoring
Behavioral tracking and intelligence gathering help identify signs of unrest, escape planning, or gang-related activities within the facility.Staff Integrity and Insider Risk
Regular audits and background checks help mitigate internal threats from compromised or negligent personnel who may facilitate contraband entry or unauthorized access.Perimeter Surveillance and Intrusion Trends
Analyzing past breach attempts and current vulnerabilities helps determine high-risk zones and informs adjustments to patrols, lighting, and detection coverage.External Threat Intelligence
Collaborating with local law enforcement and national security agencies supports awareness of coordinated external threats, such as drone drops, escape assistance, or organized infiltration.Technological Vulnerability Reviews
Evaluating the security of digital systems—such as access control, video management, and networked sensors—prevents exploitation by cyber or hybrid threats.Scenario-Based Testing
Simulating escape attempts, riots, or contraband smuggling operations allows facilities to assess preparedness and refine response protocols.
Comprehensive threat assessments equip correctional facilities with the insight needed to stay ahead of evolving risks—ensuring that security measures remain responsive, adaptable, and effective in both everyday operations and high-risk scenarios.
Customized Security Strategies for Correctional Facilities
Deploying the Proper Security Measures to Ensure Solid Security
Implementing tailored perimeter security solutions is essential for correctional facilities to prevent escapes, stop contraband smuggling, and ensure the safety of staff and inmates. A comprehensive strategy includes layered physical barriers, intelligent surveillance, strict access control, and evolving technology integrations.
Barrier Systems
Physical barriers serve as the first line of defense against unauthorized movement and escape attempts.
High-Security Fencing – Anti-climb and anti-cut fencing materials deter attempts to scale or breach facility perimeters. Reinforced options, such as welded wire mesh and tamper-detection enhancements, further delay intrusion and immediately alert security personnel.
Razor Wire and Deterrent Additions – Razor wire or concertina coils are often installed along the fence line to prevent climbing and add a strong psychological deterrent. These are particularly effective in high-security zones or around housing units.
Non-Lethal Electrified Fencing (Stun Fence) – Electrified fencing delivers a pulsed high-voltage shock upon contact. It is non-lethal yet highly effective in deterring escape attempts, while also triggering alarms for fast response.
Reinforced Gates and Sally Ports – Secure entry and exit points are critical in high-risk environments. Dual-gate sally ports, crash-rated vehicle barriers, and controlled-access portals ensure only authorized movement occurs in or out of secured zones.
Surveillance Systems
Advanced surveillance ensures real-time situational awareness across all perimeter sectors and critical facility areas.
CCTV and Video Monitoring – Cameras placed along the perimeter, towers, sally ports, and entry points enable 24/7 monitoring. Night vision, thermal imaging, and motion-triggered recording ensure visibility under all conditions.
Integrated Video Analytics – AI-powered analytics detect abnormal behavior—such as loitering, fast movement, or perimeter testing—and send real-time alerts to security teams. These systems reduce false alarms and improve response time.
Access Control Mechanisms
Strict access control helps prevent internal compromise and unauthorized access to restricted areas.
Electronic Access Systems – Biometric readers, secure PIN entry, and keycard systems help regulate movement across facility zones. Credential hierarchies limit access to only those with proper clearance.
Visitor and Contractor Management – Digital check-in systems and background screening protocols ensure all non-staff personnel are vetted and tracked. Restricted time-based access and escorted movement limit risk inside secure zones.
Integrated Technology Solutions
Evolving threats require dynamic technology that adapts to new methods of infiltration and smuggling.
Drone Detection Systems – Correctional facilities are increasingly targeted by drone drops. Detection and jamming systems help track, intercept, or disable drones before contraband reaches inmates.
Full-Body Scanners – Used at intake points and visitation areas, these scanners detect contraband hidden on or within individuals without invasive searches.
System Maintenance and Updates – Regular inspection, updates, and testing of all technology platforms ensure systems remain reliable, secure, and responsive to changing threat conditions.
By integrating these tailored strategies, correctional facilities can build a multilayered security framework—capable of defending against internal and external threats, supporting daily operations, and maintaining the integrity of high-security environments.

Developing a Comprehensive Security Plan for Correctional Institutions
Structuring a Solid Security Plan for Your Correctional Institutions
Maintaining a secure correctional facility requires more than technology and infrastructure—it depends on continuous evaluation, informed strategy, and well-prepared personnel. A successful security plan brings together routine assessments, expert collaboration, and coordinated emergency response protocols to adapt to evolving risks.
Conducting Regular Security Assessments
Routine evaluations help identify vulnerabilities and determine the effectiveness of current security measures. Assessments should result in actionable insights that lead to improved systems, updated procedures, and strengthened overall protection.
Training Personnel on Security Protocols
Educating staff in threat recognition, security procedures, and emergency response increases preparedness and confidence in high-risk situations. Ongoing drills and scenario-based training reinforce consistency and ensure swift, coordinated responses during incidents.
Collaborating with Security Experts
Working with experienced consultants provides valuable perspective in designing and updating security strategies specific to facility needs. These partnerships support implementation of best practices and emerging technologies that enhance both day-to-day and long-term security efforts.
Coordinating with Emergency Response Plans
Aligning internal protocols with local law enforcement and emergency responders strengthens incident response and recovery. Joint planning, communication channels, and shared training exercises ensure that all stakeholders are prepared to act efficiently and effectively.
By building a strategy that evolves through expert insight, hands-on training, and inter-agency coordination, correctional facilities can stay resilient in the face of complex and changing threats.
Contact Solid Security Today to See How We Can Help
Securing a correctional facility requires strategic planning and continuous vigilance. Through consistent security evaluations, specialized staff training, and guidance from trusted security experts, facilities can implement targeted solutions that prevent incidents and maintain safety. Rather than reacting to threats after they occur, take the initiative to reinforce your perimeter and ensure the stability of your operations.
Solutions for Correctional Institutions FAQ's
How do correctional facilities maintain secure perimeter boundaries?
Secure boundaries are established using a combination of high-security fencing, reinforced gates, and tamper-detection technologies. Non-lethal electrified fencing enhances security by deterring climbing or cutting, while integrated sensors and alarms provide immediate breach detection.
What makes correctional perimeter security different from other sectors?
Correctional facilities face higher risks due to the need for constant containment, internal threats, and contraband control. Their perimeter systems must be more robust and include additional safeguards like sally ports, inmate-specific protocols, and reinforced surveillance coverage.
What technologies detect tampering or breaches along the fence line?
Fence-mounted sensors, ground vibration cables, and buried detection systems monitor for climbing, cutting, or digging. These tools are integrated with surveillance and alarm systems to alert staff instantly and identify breach locations with precision.
Is it safe to use electrified fencing in correctional environments?
Yes. Non-lethal electrified fencing (NLEF) delivers controlled, pulsed high-voltage shocks that act as a deterrent without causing lasting harm. These systems comply with safety regulations and are commonly used to support secure containment.
Do drone threats pose a real risk to prison security?
Yes, drones are increasingly used to smuggle contraband. Drone detection systems identify unauthorized aerial activity using radar, RF scanning, or visual tracking, and can alert personnel or trigger automated countermeasures when threats are detected.
What response protocols should be in place for a perimeter breach?
Correctional facilities should have documented procedures that include immediate lockdowns, rapid response by trained staff, secure communication with law enforcement, and containment of affected areas. Regular drills ensure readiness in high-pressure situations.
How can large correctional perimeters be secured with limited staff?
Large perimeters can be segmented into zones using long-range cameras, sensor networks, and solar or wireless infrastructure. Centralized monitoring allows fewer personnel to oversee more ground with increased efficiency and responsiveness.
What role does video surveillance play in prison perimeter security?
Video surveillance provides real-time monitoring across the perimeter. With enhancements like thermal imaging, motion detection, and AI analytics, surveillance systems help detect threats early and verify alerts quickly for faster decision-making.
How often should correctional facilities conduct security assessments?
Assessments should be performed annually at a minimum or after any major incident. These evaluations review vulnerabilities, update procedures, and ensure that security infrastructure remains aligned with current threats and standards.
What strategies help prevent contraband from entering the facility?
Comprehensive strategies include full-body scanners, staff and visitor screening, drone detection systems, secure mail handling, and routine internal inspections. Layered enforcement helps block contraband at every potential entry point.